WSO2 Identity Server 5.11.0 - Authenticated SSTI (CVE-2025-12107)
Authenticated SSTI vulnerability found in WSO2 Identity Server 5.11.0
Evidence #
During the analysis of the application WSO2 Identity Server (version 5.11.0), I’ve identified an authenticated Server-Side Template Injection vulnerability in the extension identity-fetch-remote, which allows administrator users to fetch a configuration (in particular an XML file) from a remote location (Git repository) to automatically set up an identity provider.
Due to a weakness in the velocity engine (version 1.7.0.wso2v1), attackers are able to inject specially-crafted payloads in order to execute arbitrary code and obtain Remote Code Execution (RCE) on the affected system.
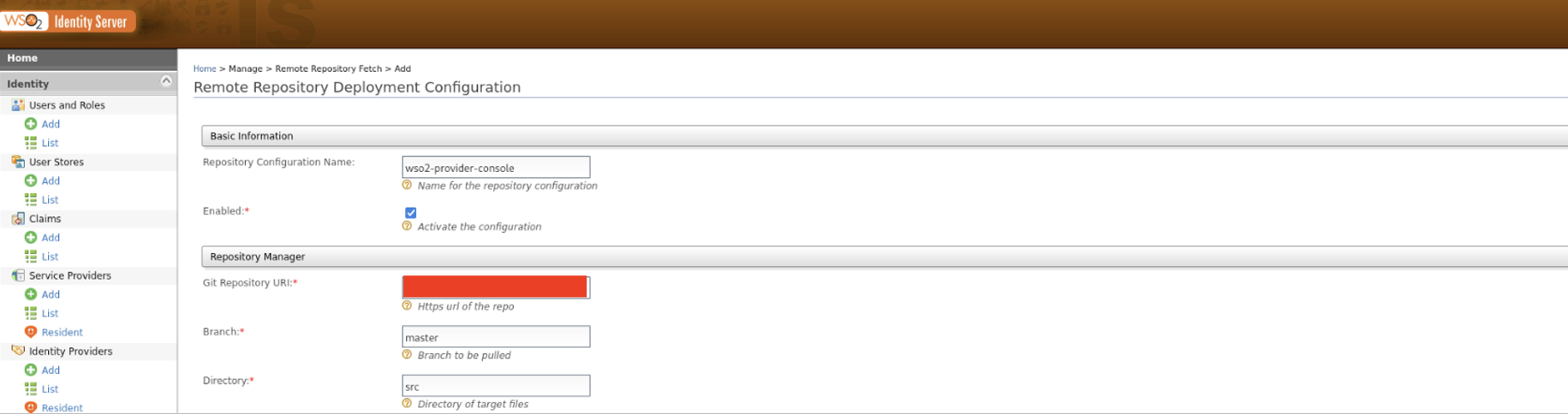
To be more specific, the interested feature can be found by navigating to the menu Home > Manage > Remote Repository Fetch > Add, as shown in the figure below.
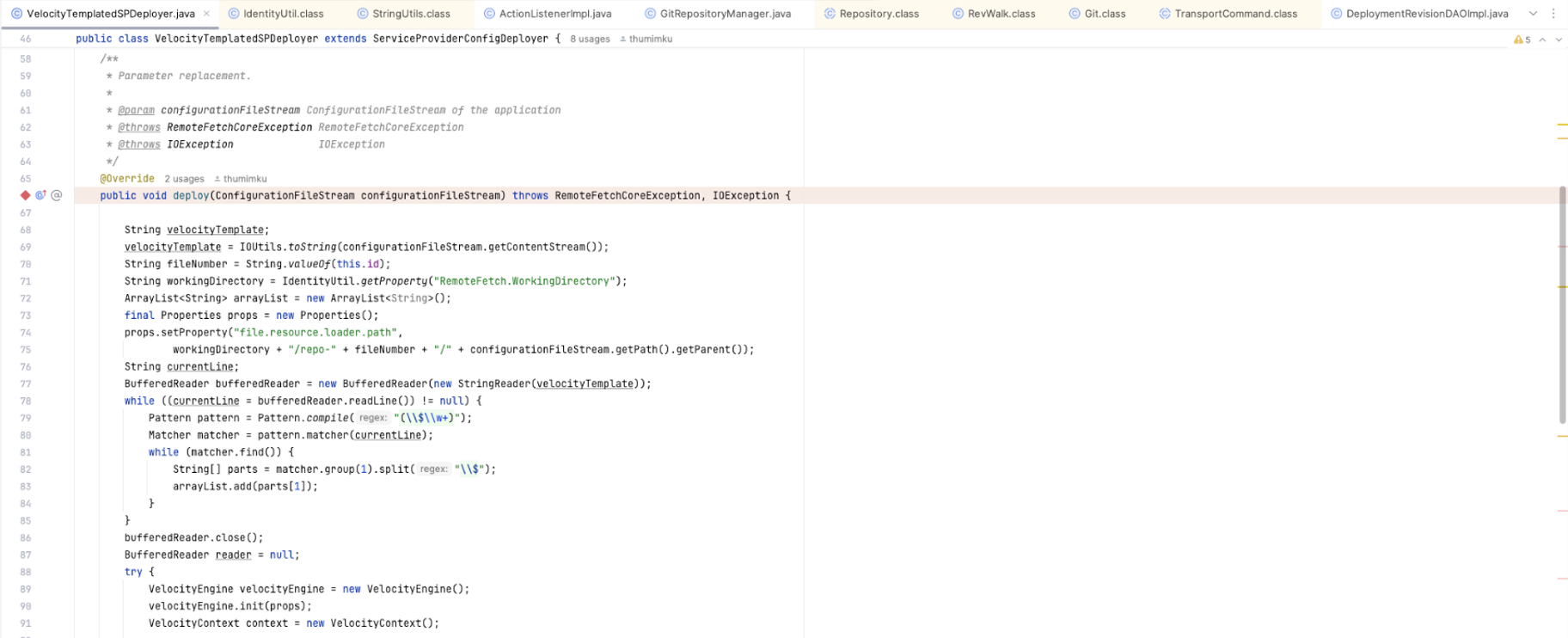
Analyzing the source code of the extension, I noticed that inside the deploy function of the VelocityTemplatedSPDeployer.java file there are no controls applied on content read from the XML file.
The two figures below show an excerpt of this file. While the lines 69 and 77 read the input XML file after fetching it from the remote Git repository, the following while loop simply populates the array arrayList (line 83), later used in conjunction with the content of the file /etc/environment (line 94) to add some parameters to the Velocity context (line 100).
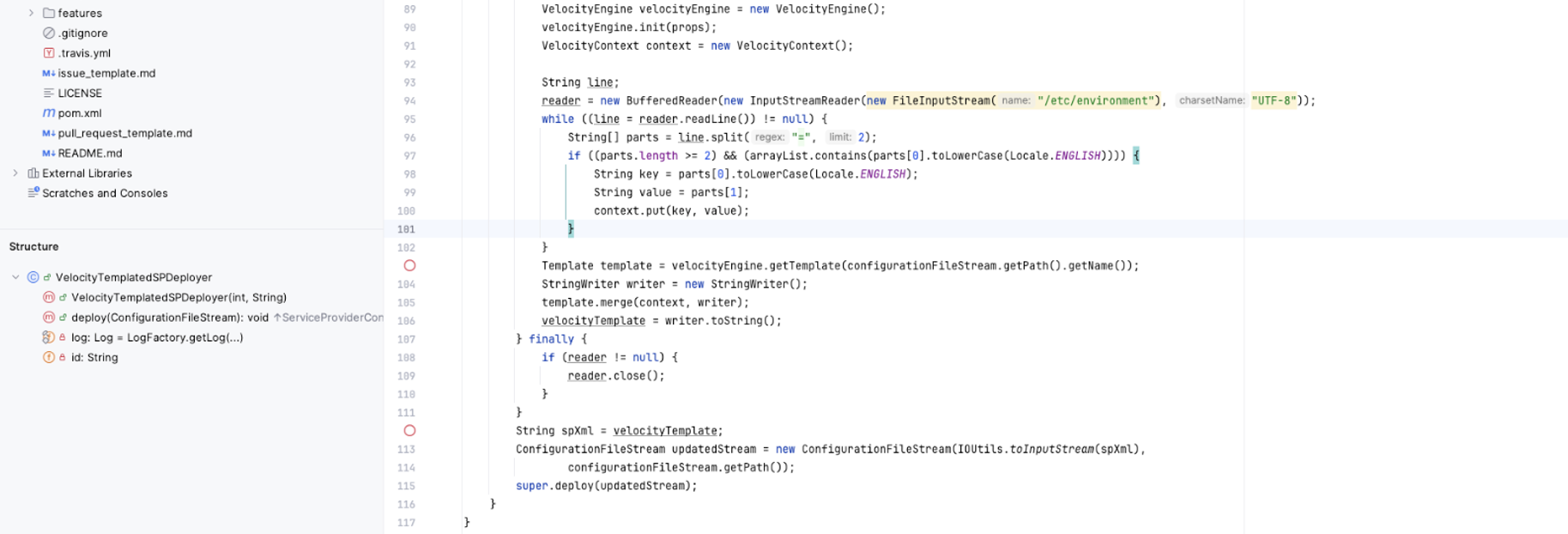
As demonstrated above, on line 103 the application uses the input XML file to populate the Velocity template; the values obtained from the previous /etc/environment file are merged on line 105.
Based on this evidence, the application does not filter the input XML file, allowing attackers to execute arbitrary Velocity templates. To test this hypothesis, I wrote a malicious template in order to spawn a reverse shell.
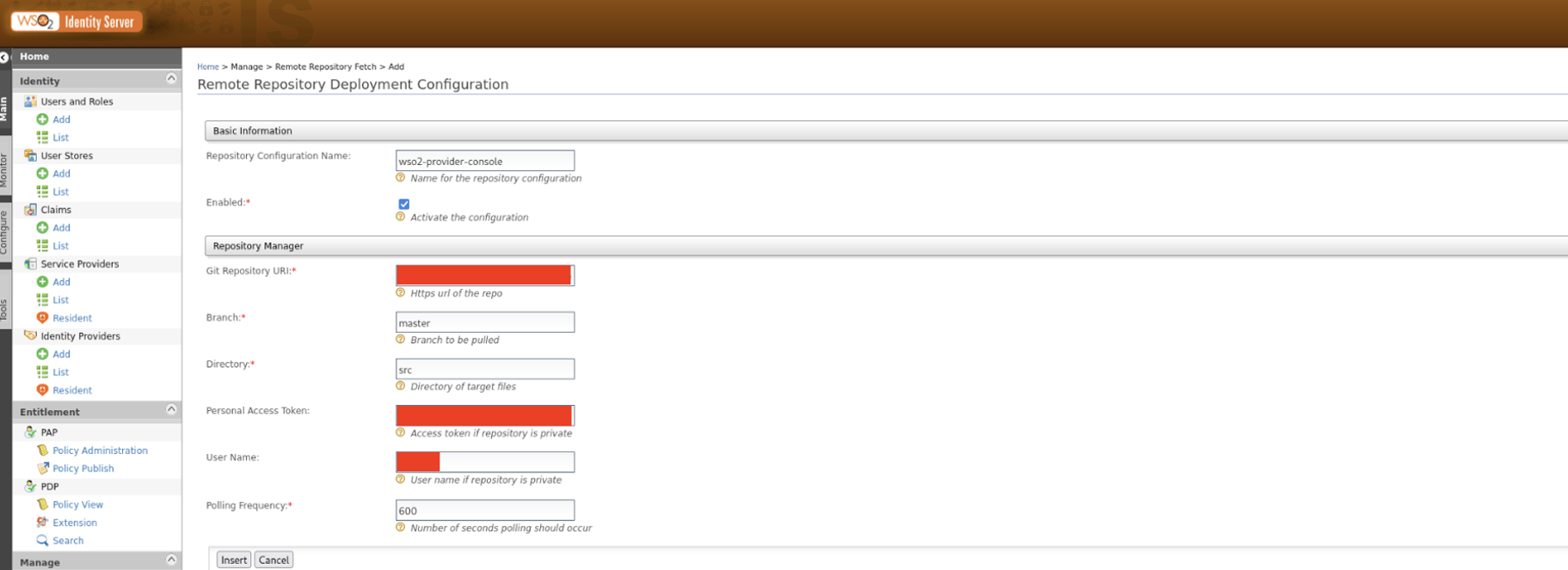
Additionally, to achieve this goal, I created a private Git repository, later configured in the vulnerable menu to be accessed by means of a Personal Access Token (PAT), as shown below.
Once successfully configured, the extension could be used to trigger the new configuration.
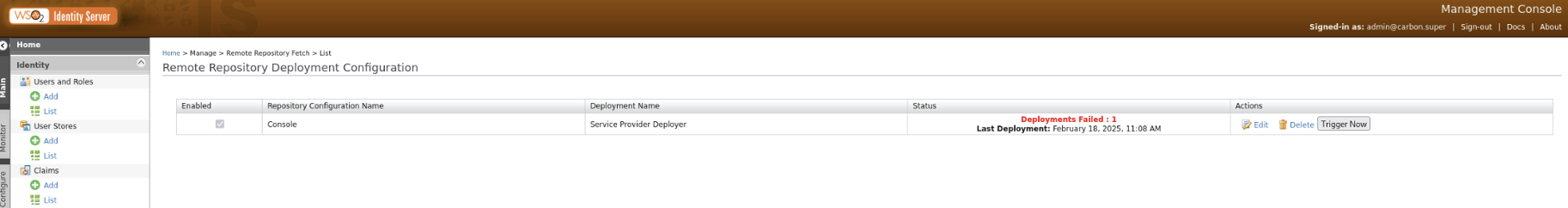
Although the screenshot above shows the failure of the given deployment, due to attempting to create an identity provider with the same name as a default one, the code was executed successfully.
The figure below shows the reverse shell obtained successfully from the victim host.
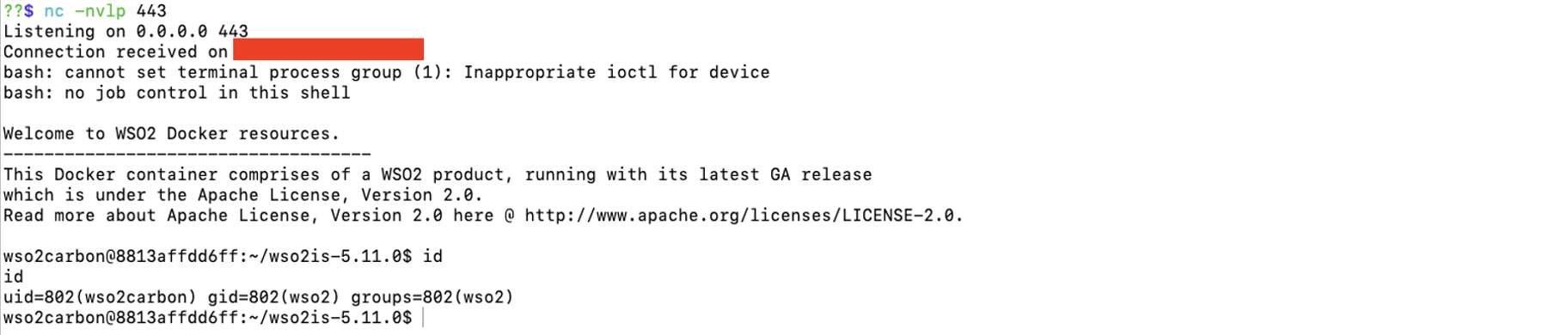
In this case, execution was obtained in the context of a Docker container. However, if the victim application was running on a system without a proper sandbox, the attacker would be able to escalate privileges and perform enumeration of the underlying system, based on the context associated with the running process.
References #
The vendor has published an advisory at the following link: WSO2-2025-4517.
You can also find information about the CVE here: CVE-2025-12107.
Vulnerability Disclosure Timeline #
| Date | Event |
|---|---|
| 2025-08-28 | Report sent to the the WSO2 security team |
| 2025-08-28 | Received response from the WSO2 security team, who started investigating the issue |
| 2026-01-10 | Requested an update from the vendor |
| 2026-02-02 | Vendor asked to delay the disclosure to allow the correct patching of the issue |
| 2026-03-06 | Vendor released the advisory for the vulnerability |
| 2026-03-11 | Received Certificate of Appreciation and added to Acknowledgements page |